Facebook在iPhone备份中存储不安全的身份验证令牌

在过去一个月左右的时间里,一些iOS应用程序一直受到安全漏洞和iPhone跟踪的关注 。现在轮到Facebook了,虽然这个问题适用于许多其他社交网站,如LinkedIn,Dropbox和使用这些网站对iOS用户进行身份验证的应用程序。
安全研究员Gareth Wright发现Facebook的iOS应用程序在纯文本文件中保存身份验证令牌。这些令牌等同于您用于登录的密码。
在备份中存储身份验证令牌不一定是个坏主意。毕竟,如果你必须从备份恢复你的手机,很高兴看到所有登录的状态,并且令牌是必要的。你可以看到它如何与Facebook的当前实现一起工作:
- 登录iPhone上的Facebook应用程序,然后使用iTunes备份
- 退出iPhone上的Facebook应用程序(转到左侧菜单底部,然后单击
Settings→Log Out - 将iTunes备份还原到手机
你会看到你重新登录。整洁。
地狱之路铺好了意图
Facebook是否将其身份验证令牌存储在备份中并不是主要问题。这里最大的问题是令牌未加密 , 没有特定于设备的元素 ,并且没有时间限制 。这意味着有人可以从备份中提取文件并将其导入自己的设备。简单来说,任何能够访问此文件的人都可以完全访问您的Facebook帐户,并使用它来窃取您的身份或跟踪您的活动。
除此之外,许多第三方应用和服务使用Facebook作为身份验证服务。如果黑客已经登录到您的Facebook帐户,他们也可以使用它来访问这些服务。
Facebook已回复新闻机构发表以下评论,尽管他们似乎忽略了不安全的备份黑客攻击的可能性,我们认为这是最简单的方法。
Facebook的iOS和Android应用程序仅用于制造商提供的操作系统,并且访问令牌只有在修改了他们的移动操作系统(即越狱的iOS或改装的Android)或授予恶意行为者访问物理设备时才容易受到攻击。我们在未修改版本的移动操作系统上开发和测试我们的应用程序,并依赖本机保护作为开发,部署和安全的基础,所有这些都在越狱设备上受到损害。正如苹果公司所说,“未经授权的iOS修改可能会让黑客窃取个人信息......或者引入恶意软件或病毒。”为了保护自己,我们建议所有用户不要修改他们的移动操作系统,以防止任何应用程序不稳定或安全问题。
你应该担心吗?要获取此文件,此人必须能够物理访问您的iOS设备或具有未加密存储备份的PC。一个随意的黑客可能无法访问这些,但一个坚定的黑客可能能够安排这样的访问。
显然,Facebook等应用发布商可以帮助自己完成以下工作:
- 对备份中的身份验证令牌应用其他加密
- 确保令牌具有特定于设备的元素,以便它们不能在其他设备上使用
- 将令牌设置为在不久的将来具有到期日期
- 通过恢复的令牌向用户提醒新登录服务
想要检查自己的Facebook身份验证令牌?
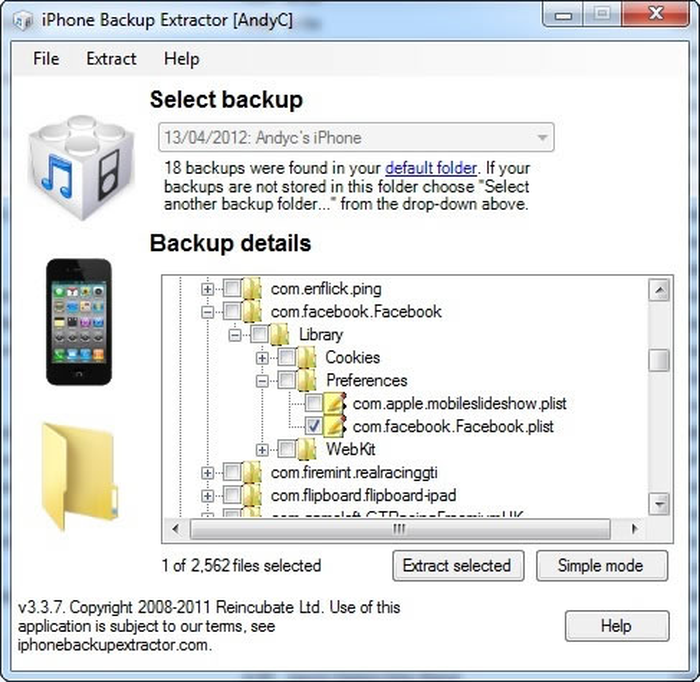
您可以使用iPhone备份提取器执行此操作,并在“专家模式”下访问备份。除非您知道自己在做什么,否则您将无法读取数据或使用它来登录Facebook - 我们已经隐瞒了出于安全原因而发布的如何执行此操作 - 但这并不需要太多想办法。

